Machine Translation
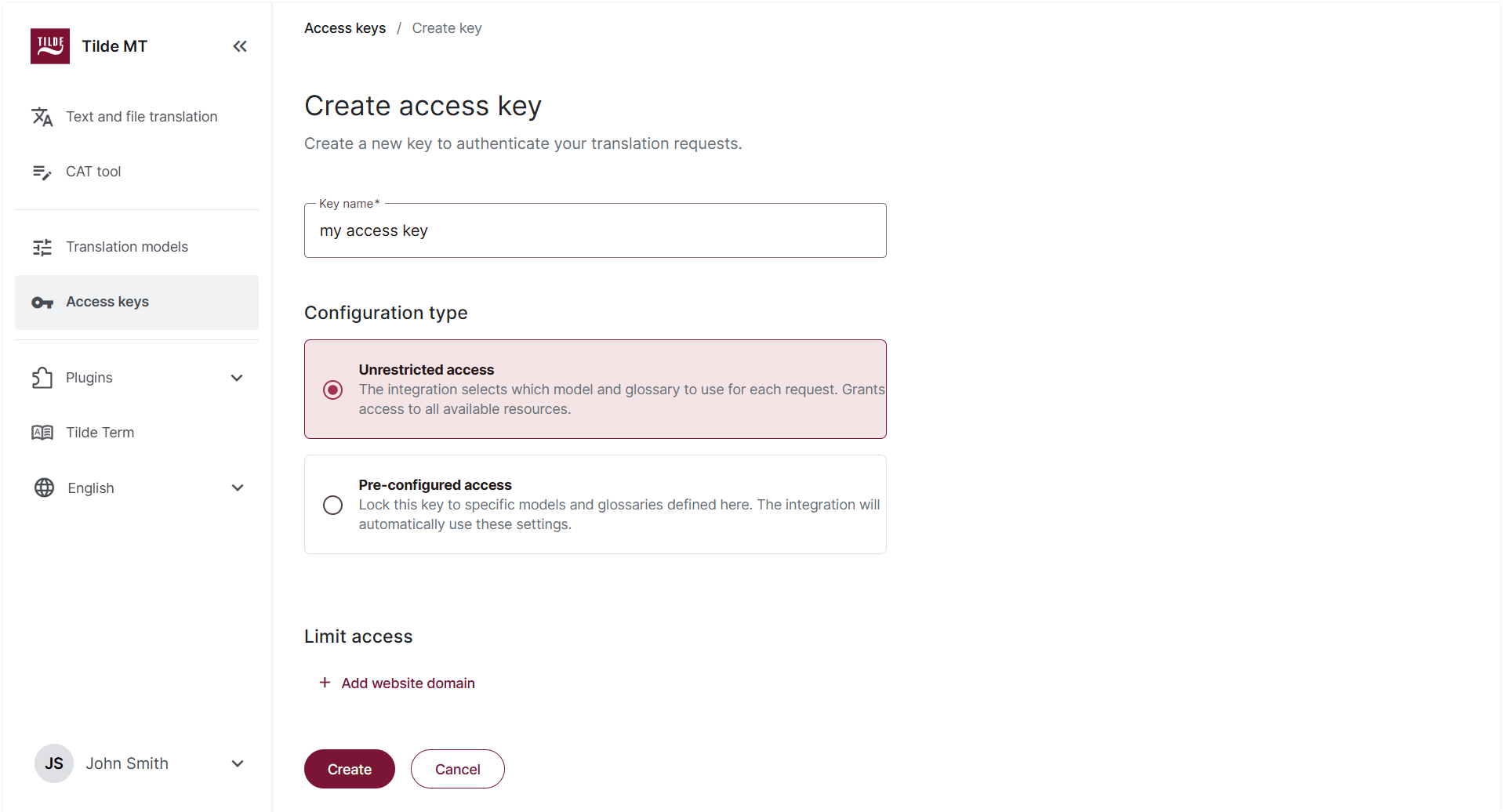
Figure 1. Unrestricted key
Figure 2. Restricted key
Access keys
Access keys authenticate external integrations with Tilde MT, including CAT tool plugins, Tilde TranslateBox, and API integrations.
Each key defines the scope of access to:
- Language directions,
- Translation models,
- Glossaries,
- Optional domain restrictions (API only),
- Keys can be configured with unrestricted or predefined scope.
Key types
Unrestricted access
The integration determines which model and glossary to use per request.
Characteristics:
- Access to all available language directions.
- Model selection controlled by the integration.
- Glossary selection controlled by the integration.
- Suitable for dynamic or centrally managed systems.
Use when:
- The integration handles configuration logic.
- Multiple projects share one key.
- Flexibility is required.
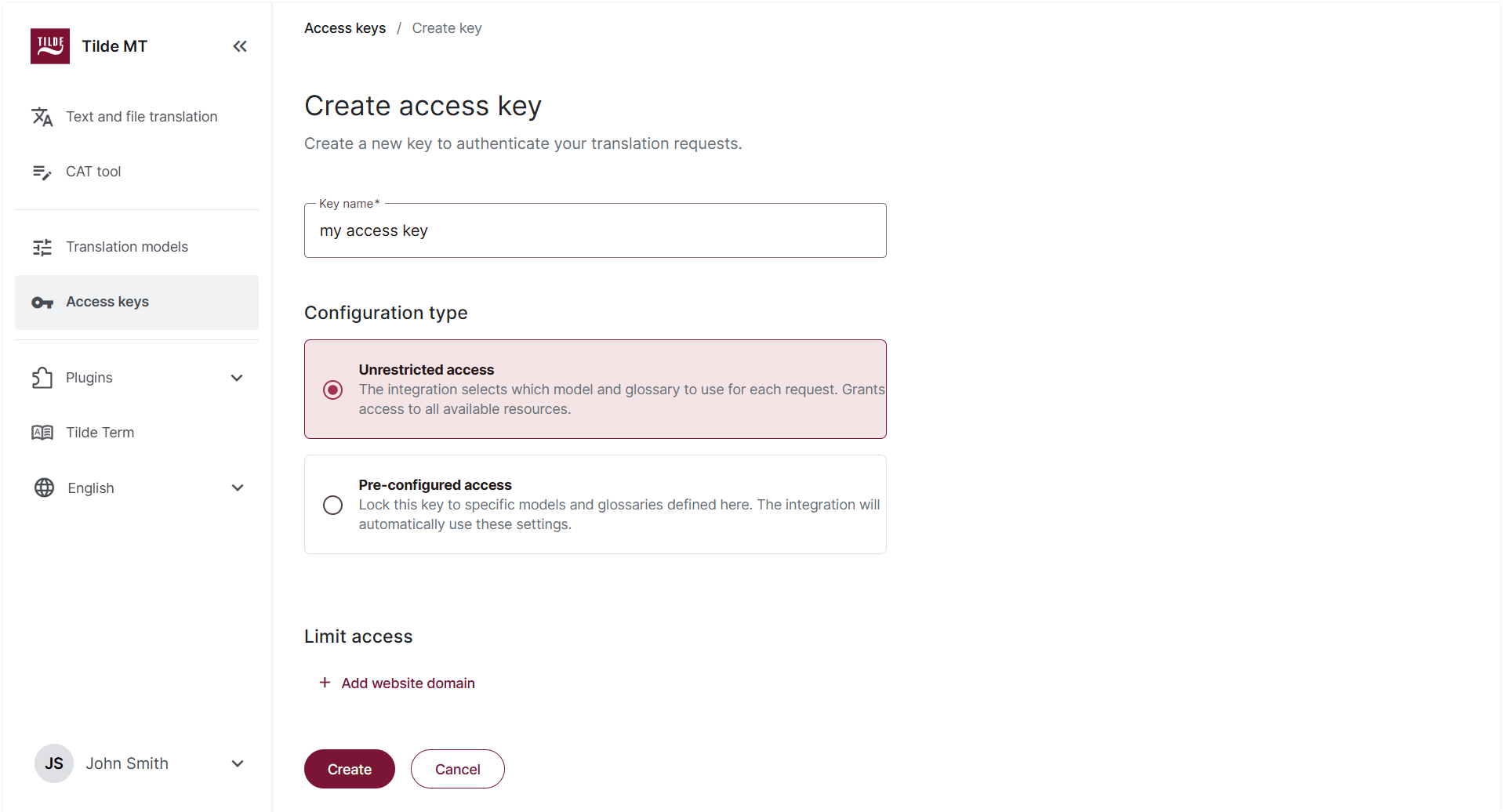
Pre-configured access
The key enforces predefined language directions, models, and glossaries.
Characteristics:
- Only configured language pairs are available.
- A specific model is enforced per language direction.
- A glossary can be enforced.
- Configuration cannot be overridden by the integration.
Use when:
- Terminology must be controlled.
- Model usage must be restricted.
- A client-specific setup is required.
- Compliance constraints apply.
Domain restriction (API)
Keys used in web-based integrations can be restricted to specific domains.
Requests originating from non-authorized domains are rejected.
Recommended for:
- Public-facing integrations.
- Embedded website translation.
- Security-controlled environments.
Lifecycle management
Create key
Define name and configuration scope.
Edit key
Modify language directions, models, glossaries, or domain restrictions. Changes apply immediately.
Delete key
Revokes access permanently. Deleted keys cannot be restored.
Security recommendations
- Store keys securely.
- Do not expose keys in client-side applications.
- Use pre-configured keys to enforce governance.
- Restrict API keys to known domains whenever possible.
- Rotate keys periodically in production environments.